...
Software Composition Analysis (SCA) and Software Bill of Materials (SBOM) Generation
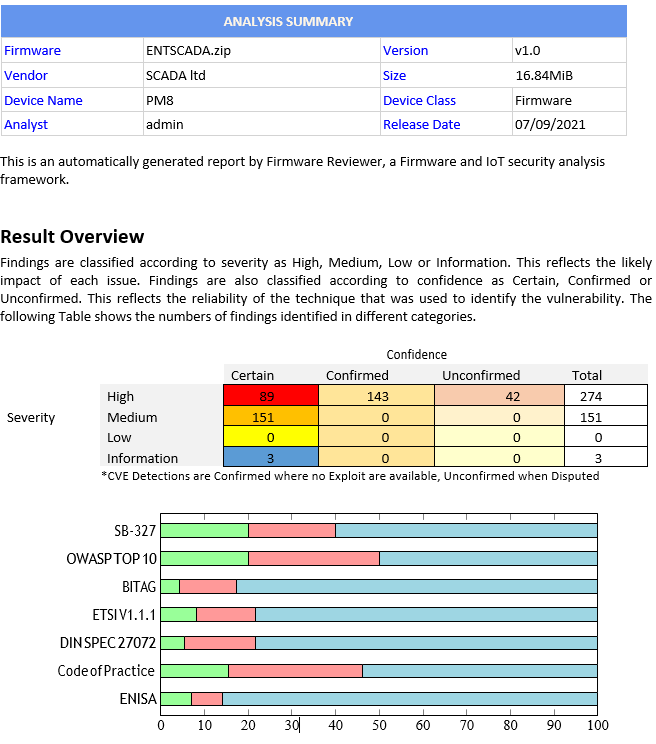
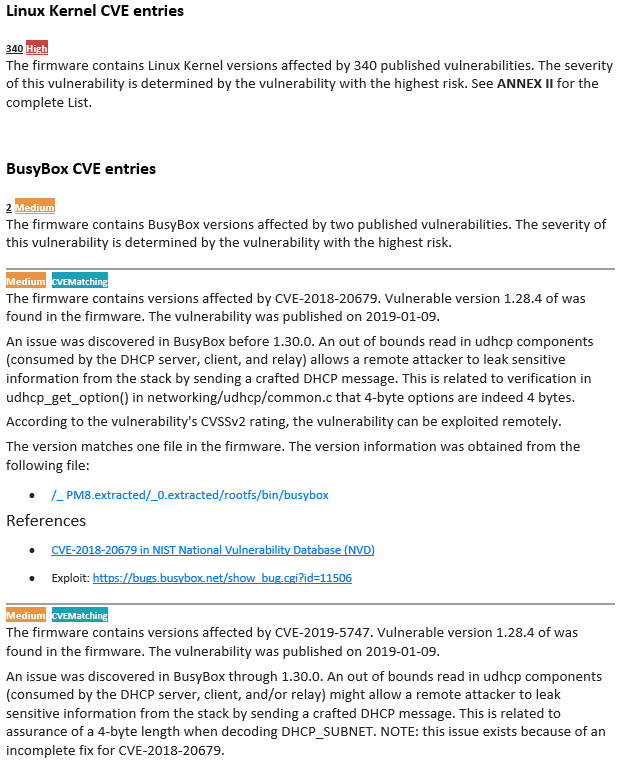
Known Vulnerabilities (CVEs)
Unknown vulnerabilities (zero-day vulnerabilities)
Compliance analysis with several supported standards and guidelines across verticals
...
The Compliance Analysis includes:
OWASP TOP 10 INTERNET OF THINGS 2018 and OWASP IoT Security Verification Standard and Embedded Best Practices
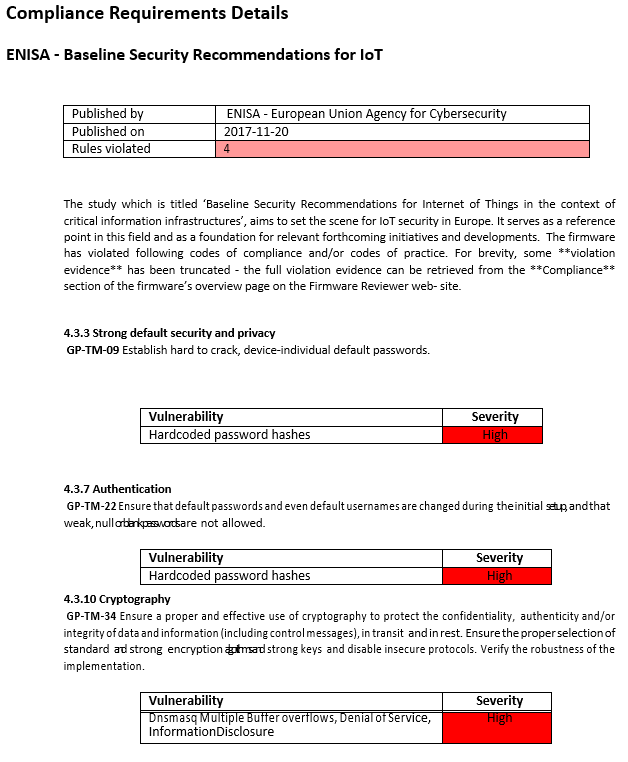
ENISA - Baseline Security Recommendations for IoT and Guidelines for Securing the Internet of Things
DCMS GOV.UK - Code of Practice for consumer IoT security
ETSI TS 103 645 V1.1.1 - Cyber Security for Consumer Internet of Things and Cyber Security for Consumer Internet of Things: Baseline Requirements
CSDE C2 Consensus on IoT Device Security Baseline Capabilities
Automotive Grade Linux Software Defined Connected Car
CISCO-NSA Router Security Configuration Guide
Executive Summary
...
Report
In case you choose to analyze your Firmware source code too, the following compliance standard will be verified:
DISCLAIMER: Firmware RevImage Image Check never operates on physical devices.
...