Firmware Reviewer Cloud Service provides in-depth firmware analysis (binaries, file systems, containers, virtual machines, IoT, UEFI, Appliances, Network Devices, Smart Meters, Surveillance devices, Drones, etc.), allowing to explore vulnerabilities at the same time to keeping the software securely in your own hands, for your eyes only. It can be used for a bunch of binary file formats, withNo need of related physical device. Further, we offer a Firmware Image Check certification.
| View file | ||
|---|---|---|
|
Quick Overview in PDF Format.
Firmware Reviewer is part of Security Reviewer Suite.
...
Main Topics
| Table of Contents | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|
|
Task Automation
Firmware analysis is a tough challenge with a lot of tasks, completely automated by Firmware Reviewer, either with new approaches or incorporation of existing tools, so that a security analyst can focus on his main task: Analyzing the firmware (and finding vulnerabilities).
...
It is available in Cloud only. For further explanation, please take a look to FAQ section.
System Requirements
Firmware Reviewer is a Cloud service accessible via Internet through a Standard Browser. Latest versions of Edge Chromium, Google Chrome and Mozilla FireFox are supported.
...
Minimum RAM: 4GB (8GB is recommended)
CPU Cores: 2 (4 is recommended)
Free Disk Space: the minimum required by your browser. In case the Client App is used, you need triple the size of your Firmware Image available on your disk.
Main Topics
| Table of Contents |
|---|
Cloud Service
Firmware Reviewer offers a Cloud platform for Analyzing and continuously Monitoring your Firmware images.
...
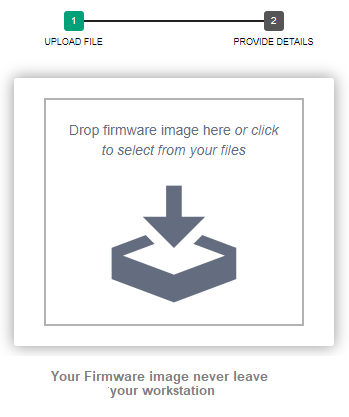
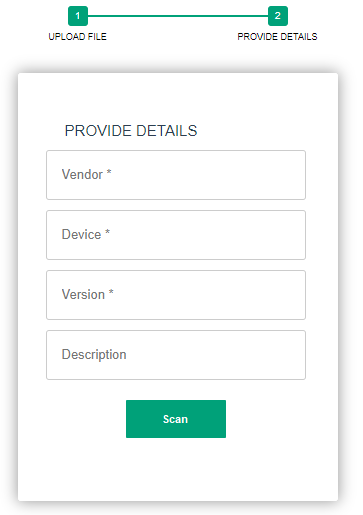
Keep your Firmware Secured
A For Linux Users, a Client App (Firmware Reviewer Submit InterfaceLocal Analyzer) is optionally available, enabling teams to scan locally.
Registered Linux Customers simply use this App for retrieving image’s relevant information and send it encrypted to Firmware Reviewer engine.
...
Firmware images won’t be uploaded to the internet
Firmware images never leave your workstation.
Firmware Analysis' Results and Reports will be stored and downloaded using AES-256 encryption.
Nor the Cloud server administrator can access the results and reports.
The encryption key is known only by you.
Compliance
Firmware Reviewer provides Reports compliant to:
OWASP TOP 10 INTERNET OF THINGS 2018 and OWASP IoT Security Verification Standard and Embedded Best Practices
ENISA - Baseline Security Recommendations for IoT and Guidelines for Securing the Internet of Things
ETSI TS 103 645 V1.1.1 - Cyber Security for Consumer Internet of Things and Cyber Security for Consumer Internet of Things: Baseline Requirements
CSDE C2 Consensus on IoT Device Security Baseline Capabilities
CVE Common Vulnerabilities and Exposures
CWE Common Weakeness Enumeration
CVSSCommon Vulnerability Scoring System
IoT
With widespread publicity of the Internet of Things (IoT), more and more devices are becoming network connected evidencing how essential it is to create secure coding guidelines for embedded software. Embedded Application Security is often not a high priority for embedded developers when they are producing devices such as routers, managed switches, medical devices, Industrial Control Systems (ICS), VoIP phones, IoT devices, and ATM Kiosks due to other challenges outside of development. Other challenges developers face may include, but are not limited to, the Original Design Manufacturer (ODM) supply chain, limited memory, a small stack, and the challenge of pushing firmware updates securely to an endpoint.
...
Firmware Reviewer results are enriched with threat intelligence from Shodan and the NIST NVD.
Supported Devices
Firmware Reviewer has been tested with the following devices types:
3D-Printers
Appliances
Base Stations
Biometric
BIOS
Cameras
Drones
Industry 4.0 Devices
IoT Gateways
Mobile
Network (Consumer, Core, Radio)
Receivers
Satellite
SCADA-PLC-PAC
Smart Meters
Smart TV
Surveillance (Home, Industry, Government, Banking)
Supported Vendors
Firmware Reviewer supports several file types:
...
Further, eCos hardware is supported. Some of the types might seem curious. E.g. postscript while being used for text mainly is seen as container for update formats of printer firmware.
Firmware Security Testing Methodology
The OWASP Firmware Security Testing Methodology is composed of nine stages tailored to enable security researchers, software developers, consultants, hobbyists, and Information Security professionals with conducting firmware security assessments. Firmware analysis is a tough challenge with a lot of tasks. Many of these tasks can be automated (either with new approaches or incorporation of existing tools) so that a security analyst can focus on its main task: Analyzing the firmware (and finding vulnerabilities). Firmware Reviewer implements this automation leading to more complete analysis as well as a massive speedup in vulnerability hunting and is able to assist you during all the nine stages:
...
There is obviously no silver bullet (read tool) that can cover (test) the whole Firmware/IoT eco-system attack surface. Our aim is to reach as close as possible i.e. to cover as many Firmware/IoT protocols, hardware platforms and products as possible. We will explain the coverage of the framework based on protocols and technologies including the what, why and how of each plugin.
Code Of Practice
In October 2018, Government of UK published code of practice for IoT vendors to improve the security of consumer IoT products, The document listed 13 guidelines for consumer IoT devices that are connected to the Internet and/or home network such as smart cameras, TVs, home appliances and home automation systems. The GOV.UK guidelines can also be mapped to several industry standards and best practices on IoT security that includes ENISA and IoT Security Foundation. A detailed mapping between these guidelines has been published in a separate document. The following guidelines were concerned with secure firmware development:
Firmware Reviewer automatically addresses those UK Government Guidelines. However, there have been different IoT Security guidelines published by different parties as good practices or baselines while there is no global standard for IoT Device Security, which as a result has created confusions in both vendors and users. They not only know which guidelines they should follow or which practices they should apply but also find a significant number of the practices impractical or irrelevant to their cases.
Unique Features
Analyze files on multiple different environments in parallel
Use any prepared image to detect APTs and harden against evasive malware
Unique, Highly configurable Hybrid Analysis Technology that analyzes full process memory
Extensive third-party integrations (e.g. IP cross-reference checks, whitelisting)
Advanced anti-analysis detection (e.g. action scripts that simulate human behavior)
Threat Score (quickly understand the malicious impact of your artifact), further to Compliance Standards
Compare between different versions
Supported
...
CPUs
Firmware Reviewer supports the following CPU Architectures:
| Code Block |
|---|
'ARM': ['ARM'],
'AARCH64': ['aarch64'],
'PPC': ['PowerPC', 'PPC'],
'MIPS': ['MIPS'],
'x86': ['x86', '80386', '80486', 'i386'],
'SPARC': ['SPARC'],
'RISC': ['RISC', 'RS6000', '80960', '80860'],
'S/390': ['IBM S/390', 's390'],
'SuperH': ['Renesas SH', 'sh4', 'sh4eb'],
'Alpha': ['Alpha'],
'hppa': ['hppa', 'pa-risc'],
'sb4': ['sb4'],
'ia64': ['ia64', 'itanium', 'ia-64'],
'cuda': ['cuda'],
'avr': ['avr', 'atmel', 'Atmega32A'],
'dlx': ['DLX'],
'mico': ['mico32'],
'mmix': ['MMIX'],
'M68K': ['m68k', '68020'] |
Supported Platforms
Firmware Reviewer analyzes cyber threats on:
...
Windows (XP, Vista, W7, W7 x64, W8, W10)
Linux (RedHat, CentOS, Fedora, Ubuntu, Debian, FreeBSD, NetBSD, and OpenBSD)
Unix (A/UX, AIX, HP-UX, illumos, IRIX, OpenServer, Solaris, Tru64 UNIX)
Mac OSX
Android
iOS
Supported File Systems
Firmware Reviewer is able to analyze several file systems like:
...
The main idea is to provide a tool for rapid analysis of filesystem images as part of a firmware security. Firmware Reviewer takes a configuration file that defines various rules for files and directories and runs the configured checks against a given filesystem image.
...
Supported Protocols
Further to NRF24, Wifi, and IP-networking, the following protocol are supported:
AMQP
BACNet
Bluetooth LE
CANBus
CoAP
DICOM
DNP3
DNS
HL7
I2C
LoRA
mDNS
Modbus
MQTT
NFC
ProfiBus
RFID
SPI
SSH
UART
UDP
UPnP
XMPP
WebSocket
Wireless HART
Zigbee
Zwave
Comparison between Versions
The File Compare check is a mechanism to compare a file from a previous run with the file from the current run. It provides more insights into file changes, since it allows comparing two versions of a file rather than comparing only a digest. Last, the Tree Check will produce an informational output listing new files, deleted files, and modified files. Firmware Reviewer can compare several images or single files. Furthermore, Unpacking, analysis and compares are based on plug-ins guaranteeing maximal flexibility and expandability.
...
In many cases you might want to compare Firmware samples. For instance, you might want to know if and where a manufacturer fixed an issue in a new firmware version. Or you might want to know if the firmware on your device the original firmware is of provided by the manufacturer. If they differ, you want to know which parts are changed for further investigation. Again, Firmware Reviewer is able to automate many of these challenges, like: Identify changed / equal files and Identify changed software versions.
Find other affected Firmware Images
If you find a new vulnerability or a new container format, you might want to know if other firmware images share your finding. Therefore, FIrmware Reviewer stores all firmware files and analysis results in a searchable database visible to authorized users only. You can search for byte patterns on all unpacked files as well as any kind of analysis result.
Accuracy
For validating our result’s accuracy, we have developed a fully automated framework and used it to test vulnerability discovery at large scale. Our system was able to find statically 38 new vulnerabilities for each of 16785 firmware packages. In addition to this, our system was able to discover dynamically 225 high-impact vulnerabilities (OWASP IoT Top Ten 2018) in at least 20% of emulated embedded web interfaces.
...
In our evaluation, we used the score fusion technique to improve the accuracy of identification. The Score Fusion technique is widely and actively used in various research fields, such as biometrics and sensors data. It is used to increase the confidence in the results and to counter the effect of imprecisely approximated data (e.g., fingerprints in biometrics) and unstable data readings (e.g., sensors data). We take as input the decreasingly ordered rankings from each of the scoring systems described above. Then, we apply majority voting to each ranking from these three scoring systems. This allows our system to decide which match is the most accurate based on its scores computed using the three different scoring systems.
DISCLAIMER: Firmware Reviewer never operates on physical devices. Security Reviewer declines all responsabilities derived by inappropriate use of Firmware Reviewer software.
...
Firmware Reviewer Security Policy
Firmware Reviewer Cloud Service provides in-depth firmware analysis via Web GUI. Does not require installation on client-side. It needs a Web Browser only.
Firmware Reviewer does not require the Firmware source code.
Users must download the Firmware image themselves. Firmware Reviewer never access to physical devices.
Our Cloud infrastructure guaranteed to stay always up to date on Firmware Vulnerabilities analysis, while maintaining your data secured.
Firmware Reviewer does not handle Sensitive or Personal Data. Usernames are represented by a sequence of alphanumeric characters from which is impossible to reveal information about the real Users. Once the Users got their Username and Password, they can login and Upload the Firmware Image they want to analyze.
The Firmware Image will be encrypted using AES-256, Uploaded using TLS 1.3 secure protocol and stored in a crypted DB Table.
Before Uploading, it is mandatory for the User to accept a Disclaimer to avoid improper use of Analysis’ Results and Reports, and to confirm the User is fully authorized by the Customer and by the Vendor (the Firmware owner).
The Analysis Results will be available between 48 hours from the Upload.
Temporary files and intermediate data, generated during the analysis, even intercepted, do not permit to reverse engineering neither the Firmware Image, nor the Analysis’ Results. They will be securely removed on each Analysis’ step.
The Analysis’ Results and Reports won’t be shared to anyone else, further than authorized internal Users. They won’t be visible neither fully nor partially on the Internet, neither on Social Media, nor in Electronic nor in Paper publications.
Analysis’ Results and Reports will be stored in crypted DB Tables, even intercepted, it will be impossible to relate them to the original Firmware Image.
Not the Firmware Reviewer Cloud Service administrator can download Firmware Images, Results and Reports, without express, written, authorization by Customer.
Users, once the Reports has been downloaded, can decide to erase them or not. The same for Analysis’ Results.
DISCLAIMER: Firmware Reviewer never operates on physical devices. Security Reviewer declines all responsabilities derived by inappropriate use of Firmware Reviewer software.